Public-key cryptography, also known as asymmetric
cryptography, is a form of cryptography in which the key used to encrypt a
message differs from the key used to decrypt it. In public key cryptography, a user has a pair of cryptographic keys - a
public key and a private key. The private key is kept secret, while the
public key may be widely distributed. Incoming messages would have been
encrypted with the recipient's public key and can only be decrypted with his
corresponding private key. The keys are related mathematically, but the private
key cannot be practically derived from the public key.
Conversely, secret key cryptography, also known as symmetric cryptography uses a single secret key for both encryption and decryption. To use symmetric cryptography for communication, both the sender & receiver would have to know the key beforehand, or it would have to be sent along with the message.
Conversely, secret key cryptography, also known as symmetric cryptography uses a single secret key for both encryption and decryption. To use symmetric cryptography for communication, both the sender & receiver would have to know the key beforehand, or it would have to be sent along with the message.
The two main branches of public key cryptography are:
Public key encryption— a message encrypted with a
recipient's public key cannot be decrypted by anyone except the recipient
possessing the corresponding private key. This is used to ensure confidentiality.
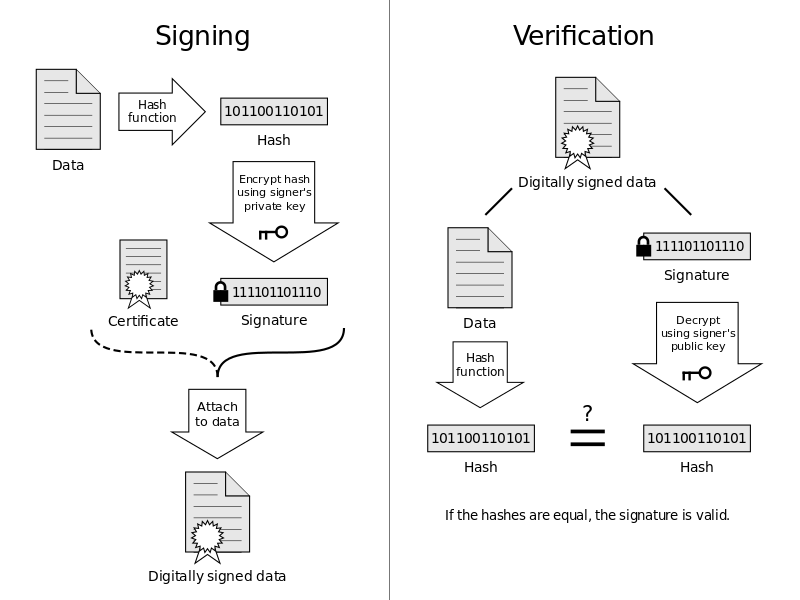
Digital signatures— a message signed with a sender's
private key can be verified by anyone who has access to the sender's public
key, thereby proving that the sender signed it and that the message has not
been tampered with. This is used to ensure authenticity.
Example 1: (Using PGP( ex: gnupgp)) - You send an encrypted message to Alice and Alice decrypts it
1. You say to PGP that it has to encrypt a message with the Alice's public key 'APK' PGP creates a new temporary secret key 'TSK' randomly
2. PGP encrypts the message by means of the temporary key 'TSK' (it uses IDEA, CAST or Triple-DES algorithms, which are symmetric systems)
3. PGP encrypts the temporary key 'TSK' by means of the Alice's public key 'APK' (it uses RSA or DSS/Diffie-Hellman algorithms, which are asymmetric systems). So this key become an encrypted key 'EK'
4. PGP sends both of them (the encrypted message and the key used to encrypt it) to the recipient Alice receives your message
5. She decrypts the encrypted key 'EK' by means of her private key 'APRIVK' (here PGP uses RSA or DSS/Diffie-Hellman algorithm). So the key become 'TSK' again
6. Now her copy of PGP 'knows' the temporary secret key 'TSK', so it can use it to decrypt the message.
Example2: Giving a .NET Assembly a Strong Name
When the compiler digitally signs an .NET assembly, it calculates a cryptographic digest of the contents of the assembly. A cryptographic digest is a fancy hash of your assembly's file contents. Let's call this cryptographic digest the compile-time digest of the assembly. The compiler encrypts the compile-time digest using the 1,024-bit private key from your public-private key pair file. The compiler then stores this encrypted compile-time digest into the assembly. Note that this all happens during development.
Sometime later, whenever the .NET loader loads an assembly with a strong name, the loader itself calculates a cryptographic digest of the contents of the assembly. Let's call this digest the runtime digest of the assembly. The loader then extracts the encrypted compile-time digest from the assembly, extracts the public key for the assembly from the assembly itself, and uses the public key to decrypt the previously encrypted compile time digest. The loader then compares the calculated runtime digest to the decrypted compile-time digest. When they are not equal, something or someone has modified the assembly since you compiled it; therefore, the runtime fails the assembly load operation.
Misc Info:
GNU Privacy Guard (GnuPG or GPG) is a free software replacement for Symantec's PGP cryptographic software suite. GnuPG is compliant with RFC 4880, which is the IETF standards track specification of OpenPGP. Modern versions of PGP and Veridis' Filecrypt are interoperable with GnuPG and other OpenPGP-compliant systems. GnuPG is part of the GNU project, and has received major funding from the German government. Libgcrypt is a cryptographic library developed as a separated module of GnuPG.[3] It can also be used independently of GnuPG, although it requires its error-reporting library.
Libgcrypt(https://www.gnu.org/software/libgcrypt/) is a general purpose cryptographic library based on the code from GnuPG. It provides functions for all cryptograhic building blocks: symmetric ciphers (AES, DES, Blowfish, CAST5, Twofish, SEED, Camellia, Arcfour), hash algorithms (MD4, MD5, RIPE-MD160, SHA-1, SHA-224, SHA-256, SHA-384, SHA-512, TIGER-192, Whirlpool), MACs (HMAC for all hash algorithms), public key algorithms (RSA, Elgamal, DSA, ECDSA), large integer functions, random numbers and a lot of supporting functions.
Secure Remote Password protocol (http://srp.stanford.edu/doc.html) => new password authentication and key-exchange protocol suitable for authenticating users and exchanging keys over an untrusted network.
The Secure Remote Password protocol performs secure remote authentication of short human-memorizable passwords and resists both passive and active network attacks. Because SRP offers this unique combination of password security, user convenience, and freedom from restrictive licenses, it is the most widely standardized protocol of its type, and as a result is being used by organizations both large and small, commercial and open-source, to secure nearly every type of human-authenticated network traffic on a variety of computing platforms.
ref:
Public Key Infrastructure(PKI) -
- http://en.wikipedia.org/wiki/Public_key_infrastructure
- http://archive.opengroup.org/public/tech/security/pki/index.htm
- http://csrc.nist.gov/groups/ST/crypto_apps_infra/pki/index.html
- http://www.oasis-open.org/committees/tc_home.php?wg_abbrev=pki
- http://datatracker.ietf.org/wg/pkix/charter/
- http://www.sun.com/blueprints/0801/publickey.pdf
Pretty Good Privacy (PGP) - http://www.rubin.ch/pgp/pgp.en.html
- Complete Secure Remote Password (SRP-6a) implementation for Java -http://grepcode.com/snapshot/repo1.maven.org/maven2/com.nimbusds/srp6a/1.4.1
- https://www.logintc.com/blog/2013-12-06-secure-remote-password.html
Junfeng Zhang's Windows Programming Notes - http://blogs.msdn.com/junfeng/archive/2006/03/11/549355.aspx
.Net Assembly digital signing - http://blogs.pingpoet.com/overflow/archive/2005/05/20/1995.aspx
.Net Assembly digital signing - http://www.csharp411.com/net-assembly-faq-part-3-strong-names-and-signing/
